Google Search and Google DNS outage
Monday, October 13th, 2014It really isn’t every day that your Google Search request fails with:
Server Error We're sorry but it appears that there has been an internal server error while processing your request. Our engineers have been notified and are working to resolve the issue. Please try again later.
My two subsequent attempts also failed with the same error, but it got back into working order after that.
I quickly searched this message on Google Search – after it was working of course – and found something else you also don’t quite see every day:
Crawled “38 secs ago”? Someone else’s discovery is definitely related.
Just minutes before however, 8.8.8.8 and 8.8.4.4 could not be reached from my location, which are usually reached in around 24ms. Over 30 minutes later, it was finally rerouted to somewhere else with a latency of 174ms. I’m not sure if these issues are related, but something has definitely gone wrong somewhere.
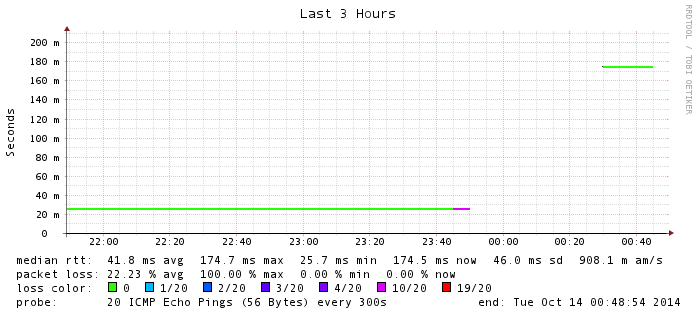
A 30-minute outage and then a reroute to a location outside of Australia.
I wouldn’t be surprised if some admins at Google were running around with their hair on fire.